Booking.com Got Breached Again. Your Front Desk Is About to Deal With It.
Booking.com just exposed guest names, emails, phone numbers, and reservation details to unauthorized third parties... and the phishing emails targeting your guests have already started. The OTA says no financial data was compromised, but the real damage isn't about credit cards.
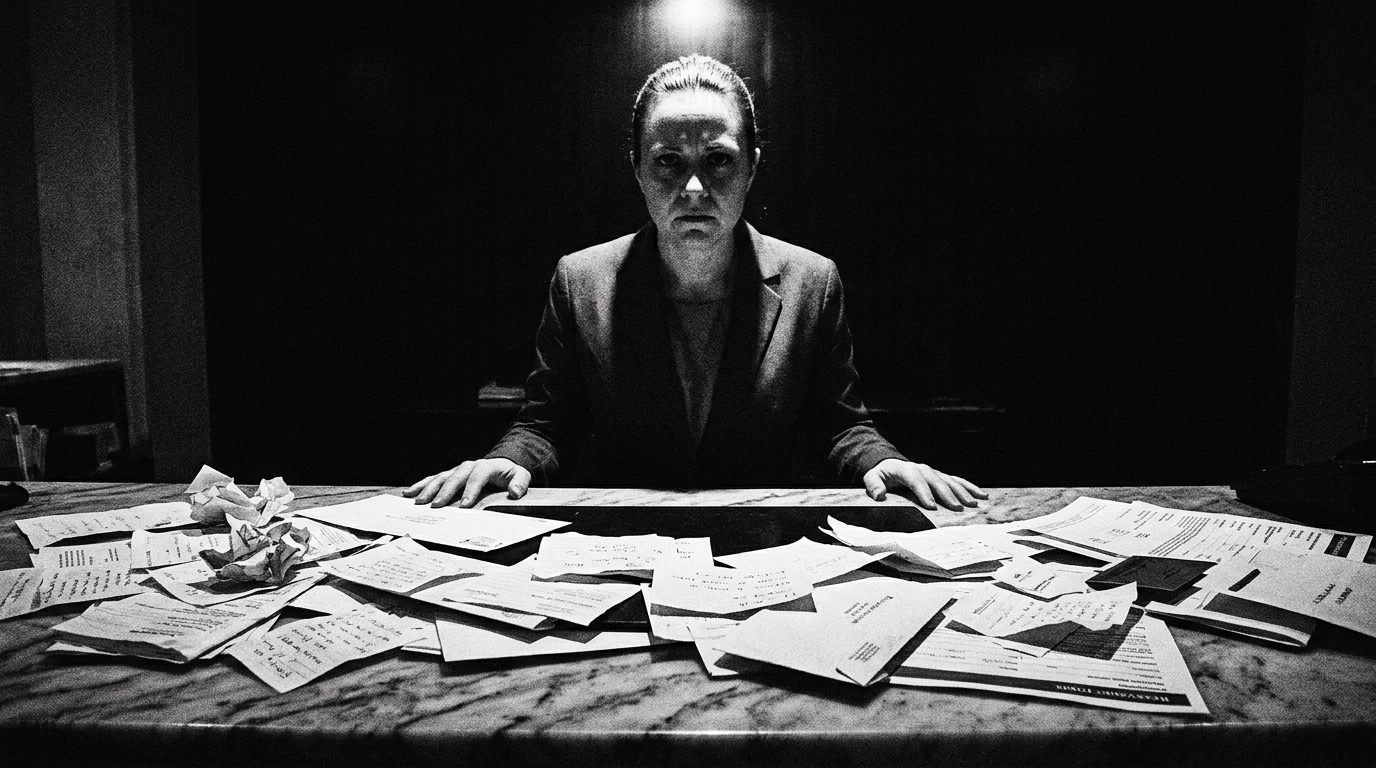
I worked with a GM years ago who kept a printed list taped to the back of the front desk... every known phone scam, every phishing email template, every variation of "I'm calling from corporate and I need you to process a refund." She updated it monthly. Her staff knew the scripts better than the scammers did. When I asked her why she went through the trouble, she said something I've never forgotten: "The guest doesn't blame the scammer. The guest blames us. Because we're the ones standing in front of them."
That's exactly what's about to happen at properties all over the country. Booking.com confirmed over the weekend that unauthorized third parties accessed guest reservation data... names, email addresses, phone numbers, booking details. They say no payment information was compromised. They've reset PINs on affected reservations and emailed impacted customers. And they won't say how many people were affected, which tells you something all by itself.
Here's what nobody's telling you about why this matters more than the headline suggests. The stolen data isn't valuable because of what it IS. It's valuable because of what it ENABLES. A scammer who knows your guest's name, their check-in date, and which hotel they're staying at can craft an email or WhatsApp message that looks indistinguishable from a legitimate hotel communication. "Dear Mr. Henderson, regarding your April 22 reservation at the Courtyard... we need to verify your payment method." Reports are already surfacing of guests receiving exactly these messages. Your guest gets that email, panics, hands over their credit card... and then calls your front desk furious because they think YOU sent it. This is the third or fourth time in three years that Booking.com's ecosystem has been the vector for this kind of attack. In 2023 it was a phishing campaign that compromised hotel partner systems and stole credit card data directly. In 2025 there was an infostealer malware campaign targeting hospitality staff through fake CAPTCHA pages. Last summer, scammers used real booking data obtained through compromised hotel accounts to send fraudulent payment requests. The pattern is clear and it's accelerating. Booking.com claims they blocked 85 million fraudulent reservations and 1.5 million phishing attempts in a single year. Good for them. But when the breaches keep happening despite those numbers, the question isn't how hard they're trying. It's whether the architecture itself is the problem.
And here's where this gets uncomfortable for operators. Booking.com's official position in several past incidents has been that their systems weren't breached... that the compromise happened through partner hotel systems. Think about that. The OTA collects the commission. The hotel absorbs the operational fallout AND potentially takes the blame for the security failure. Whether the entry point this time was Booking.com's infrastructure or a partner property's compromised credentials, it doesn't matter to the guest standing at your desk asking why someone has their reservation details. You're the face. You're the one who has to explain it. You're the one who eats the bad review.
This isn't a cybersecurity story. It's an operations story. Every front desk agent at every property that takes OTA bookings needs to know, right now, that a wave of sophisticated phishing is coming. Your guests are going to receive messages that reference real reservation data. Some of your guests are going to fall for it. And some of those guests are going to walk through your lobby door convinced that your hotel leaked their information. Because from where they're standing... that's exactly what it looks like.
If you have Booking.com reservations on the books for the next 30 days, this is your problem right now. Today... not next week... brief every front desk agent on what's happening. Give them language for when a guest calls or walks in saying "someone contacted me about my reservation." Something simple: "That did not come from us. Booking.com experienced a data incident. Never share payment information through links in emails or messages. We can verify your reservation right here." Print it. Tape it behind the desk. Second, check your own Booking.com partner portal security. Enable two-factor authentication if you haven't (Booking.com requires it for payment access but make sure it's active across all admin accounts). Change your passwords today. Third, if you're an owner with significant OTA exposure through Booking.com, this is the moment to seriously evaluate what that dependency costs you beyond the commission. This is what I call the Invisible P&L... the labor hours spent managing guest panic, the review damage from scam fallout, the trust erosion that never shows up as a line item but absolutely shows up in your repeat booking rate. You can't control what happens on their servers. But you can control how prepared your team is when the phone starts ringing.